
Cybersecurity Consulting Services
Protect What Matters Most
Create a secure environment with MMC Global cybersecurity consulting services by implementing cybersecurity protocols for your people, operations, and reputation. We help you create a strategic approach to overcome privacy challenges.
Get a Free Consultation
Trusted by industry leaders worldwide
Our Cybersecurity Consulting Services & Solutions
At MMC Global, we provide top-tier Cybersecurity Consulting Services & Solutions to help businesses identify, assess, and mitigate security risks. Our team of experienced cybersecurity professionals works closely with organizations to develop tailored security strategies that align with their goals and regulatory requirements.
Cybersecurity Consulting Services
Our expert cybersecurity consultants provide in-depth analysis and strategic guidance to bolster your cybersecurity posture. We identify vulnerabilities, recommend robust defenses, and help you navigate complex regulatory landscapes to achieve compliance.
Pentesting
Our penetration testing services simulate real-world attacks to identify and exploit vulnerabilities in your systems. By understanding your weaknesses before malicious actors do, our cybersecurity consulting services help you fortify your defenses and ensure the integrity of your network.
Managed Detection and Response
MMC Global’s MDR service offers continuous monitoring, threat detection, and incident response. Our advanced analytics and expert team work around the clock to identify and mitigate threats in real-time, minimizing potential damage and ensuring swift recovery.
Identity and Access Management Software Implementation
We provide comprehensive IAM solutions that manage user identities and control access to critical information. Our implementations ensure that only authorized personnel can access sensitive data, reducing the risk of insider threats and enhancing overall security.
50+
Expert Developers
10+
Years of Industry Experience
35+
Industries Covered
75+
Clutch Reviews
Strengthen Your Cyber Defenses
Identify risks, secure critical assets, and protect your business with expert cybersecurity consulting tailored to your needs.
Let Us Be Your Partner in Cybersecurity Challenges
At MMC Global, we understand the evolving landscape of cybersecurity threats and are committed to providing top-notch protection for your business. Here are four major reasons to choose us:
01
Comprehensive Security Solutions
We offer end-to-end cybersecurity services, including risk assessments, threat intelligence, incident response, and compliance support, ensuring your business stays protected from all angles.
02
Cutting-Edge Technology & Expertise
Our team of cybersecurity professionals leverages the latest technology, AI-driven threat detection, and industry best practices to safeguard your digital assets against ever-evolving cyber threats.
03
Customized Approach for Every Business
We understand that every business has unique security needs. Our tailored cybersecurity strategies ensure maximum protection while aligning with your organization’s goals and operational requirements.
04
24/7 Monitoring & Rapid Response
Cyber threats don’t take breaks, and neither do we. Our dedicated security teams provide round-the-clock monitoring and rapid incident response to mitigate risks before they cause harm to your business.
Our Work
We have delivered almost 1000+ projects to the world-leading companies that established our diverse portfolio to represent our massive contribution to digital transformation.
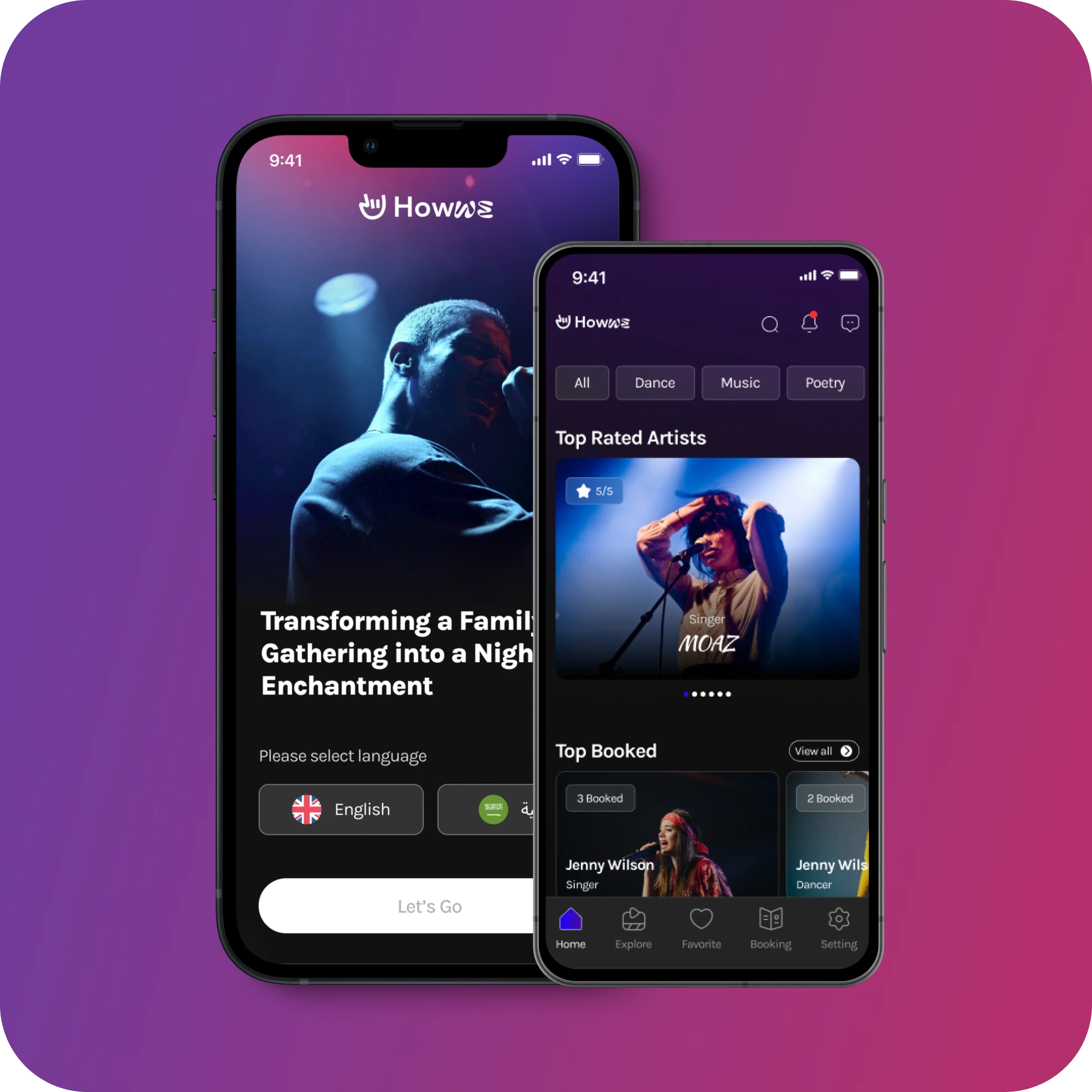
Howwe
User Research & TestingBrandingUIUX DesignDevelopment
Howwe is a music and entertainment mobile app that connects users with artists worldwide. It makes discovering, streaming, and engaging with music simple, accessible, and community-focused.
30% Outcome120% ROI200M+ Downloads
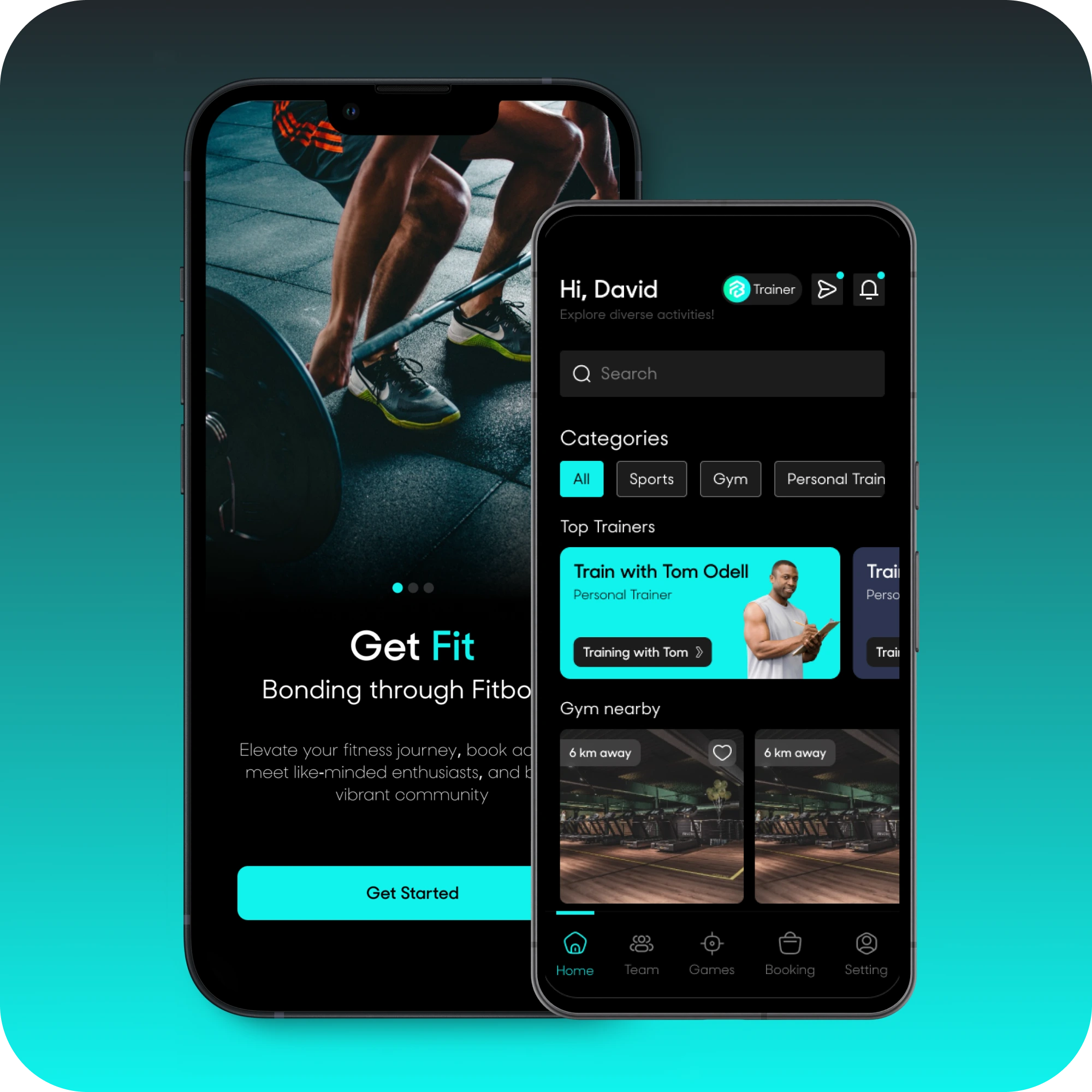
Fitbond
User Research & TestingBrandingUIUX DesignDevelopment
Fitbond is a gym and fitness app designed with a user-first approach. We handled user research, branding, UI/UX design, and development to deliver a simple, engaging, and easy-to-use fitness experience.
40% Increase in User Engagement100% Return on Investment100M+ App Downloads

RevMe
User Research & TestingBrandingUIUX DesignDevelopment
RevMe is a skill-building app that helps users develop daily living and independence skills. Through guided activities and tasks, it supports users in building confidence, self-reliance, and practical life abilities.
45% Improvement in User Outcomes95% ROI10M+ App Downloads
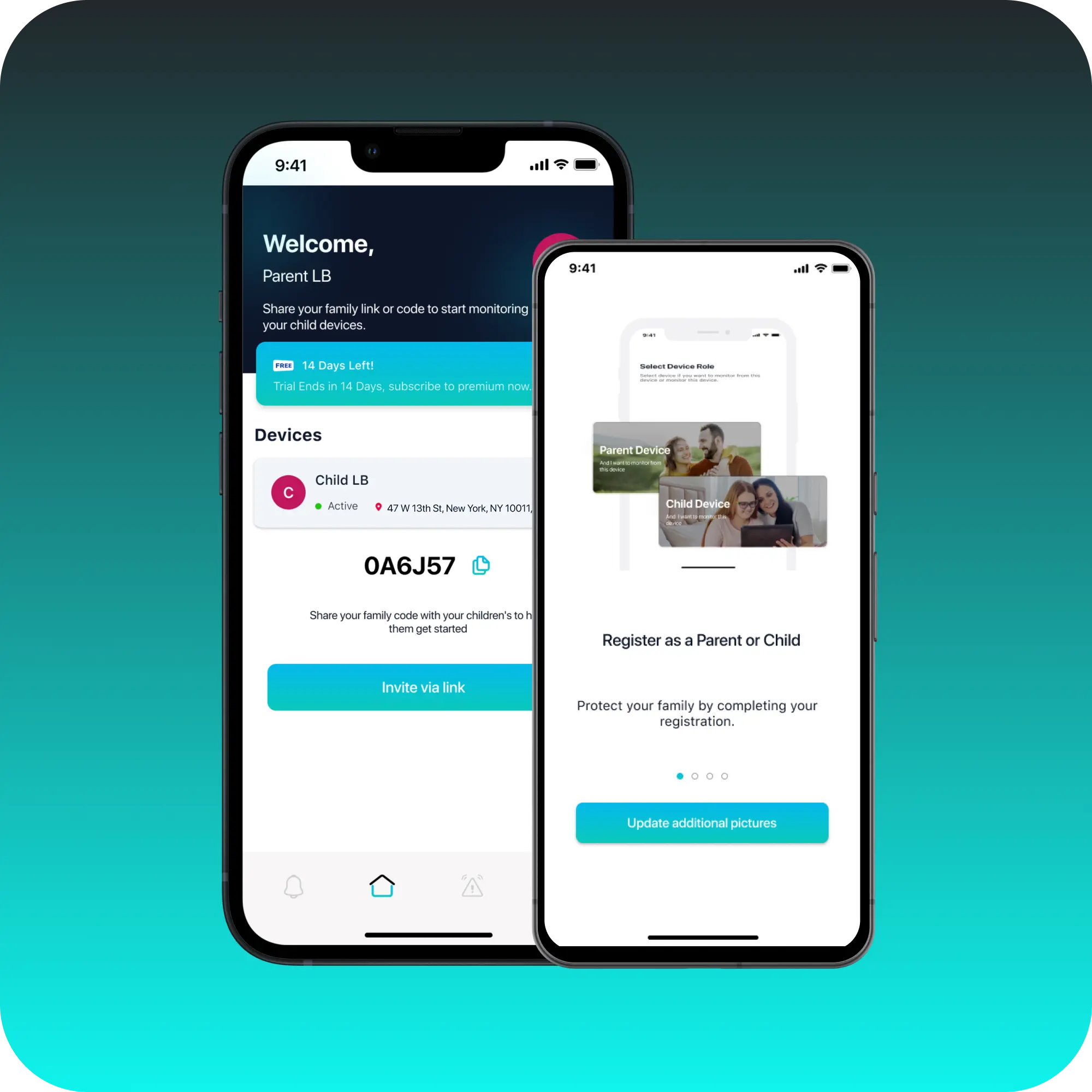
Little Bird
User Research & TestingBrandingUIUX DesignDevelopment
Little Bird is a parental monitoring mobile app designed to keep children safe online. It helps parents monitor their child’s phone activity and detects adult or inappropriate content.
60% Reduction in Inappropriate Content Exposure90% Parent Satisfaction Rate5M+ App Downloads
Acknowledgement & Recognition
Recognition reflects our efforts and support from others, inspiring us to keep striving for excellence and making an impact.
15+ reviews on Clutch
4.8

DesignRush
Top Software Development Agency

Clutch Global
Top Mobile App Developers

Microsoft Partner
Microsoft Partner Solutions

UpFirms
Top Software Development Companies

App Futura
Top Artificial Intelligence Company

Bark
Top Rated Web Development Company

Bark
Certificate of Excellence

GoodFirms
Top Project Management Software

Clutch
Top Artificial Intelligence Company

Techreviower
Top Software Developers

TopDevelopers
Top B2B Service Provider

Trustpilot
Excellent 4.8/5 Customer Rating
A Security Strategy That Fits You
Personalized Strategic Approach
We understand that cybersecurity is not a one-size-fits-all solution. Our cybersecurity consulting services are designed to provide you with personalized insights and actionable strategies. Our experienced cybersecurity consultants work closely with your team to assess your current security measures, identify potential risks, and develop a comprehensive plan tailored to your organization’s unique needs. Whether you are seeking to enhance your defenses, achieve regulatory compliance, or navigate the complexities of cybersecurity, our experts are here to guide you every step of the way.

Stay Ahead of Cyber Threats
Build a resilient security strategy to safeguard your data, operations, and reputation from evolving cyber risks.
Client Feedback That Motivates Us
Client Review
Great experience working with this excellent team for the development and launch of my App. Worked closely with key members Trevor, Jessica & Moona who all displayed diligence and constant sense of urgency. Prompt attention and quick resolution of concerns contributed to a seamless experience.
John Doe
CEO
Client Review
My experience was 5/5 and it started with customer service. After speaking with Trevor he helped me out a lot. He even sent me a few options to see what project I liked the most. He gave a timeline for when the team would complete the job I asked for and they were right on time. Will absolutely return for future projects.
Matt Connelly
CEO
Client Review
I would definitely recommend this company. Trevor Michaels, Project Coordinator was AMAZING from beginning to end. He was thorough, patient and understood the task at hand. We were truly pleased with the outcome. Thanks again Trevor for your professionalism and for providing flawless service!
Karen Popplewell
Owner
Client Review
Richard and his team did a great job contacting me and keeping me updated regarding my project. I was in the process of trying to build my project on my own, and it looked terrible; however, Richard and his team saved my project. I will keep in touch with this company when I need their help again.
Dawn Brown
Entrepreneur
Client Review
Great experience working with this excellent team for the development and launch of my App. Worked closely with key members Trevor, Jessica & Moona who all displayed diligence and constant sense of urgency. Prompt attention and quick resolution of concerns contributed to a seamless experience.
John Doe
CEO
Client Review
My experience was 5/5 and it started with customer service. After speaking with Trevor he helped me out a lot. He even sent me a few options to see what project I liked the most. He gave a timeline for when the team would complete the job I asked for and they were right on time. Will absolutely return for future projects.
Matt Connelly
CEO
Client Review
I would definitely recommend this company. Trevor Michaels, Project Coordinator was AMAZING from beginning to end. He was thorough, patient and understood the task at hand. We were truly pleased with the outcome. Thanks again Trevor for your professionalism and for providing flawless service!
Karen Popplewell
Owner
Client Review
Richard and his team did a great job contacting me and keeping me updated regarding my project. I was in the process of trying to build my project on my own, and it looked terrible; however, Richard and his team saved my project. I will keep in touch with this company when I need their help again.
Dawn Brown
Entrepreneur
Infusing Modern Technologies in Cybersecurity Implementation
Frontend
Ionic
React Native
Flutter

Xamarin

NativeScript
Angular

Framework7

Corona SDK
Backend

Laravel

Django

Ruby-on-Rails

ExpressJS

Flask
Spring

ASP.Net-Core
Database

PostgreSQL
MangoDB

MySQL

Microsoft SQL Server

DynamoDB
MariaDB
QA

Appium

XCUITest

EarlGrey

Selendroid
Design

Adobe XD
Figma

Sketch
Devops

Jenkins

Ansible
Git
Kubernetes

Docker

GitLab
Nagios

NativeScript
Our Cybersecurity Consulting Process
We follow a structured cybersecurity consulting process to assess risks, implement strong defenses, and continuously improve your security posture while aligning with your business goals.
01
Discovery & Risk Assessment
We analyze your existing security posture, infrastructure, and workflows to identify vulnerabilities, threats, and compliance gaps.
02
Strategy & Security Roadmap
Based on insights, we design a customized cybersecurity strategy with clear policies, controls, and risk mitigation plans.
03
Implementation & Hardening
Our experts deploy security measures, tools, and best practices to strengthen systems, networks, and data protection.
04
Testing & Validation
We conduct penetration testing, audits, and simulations to validate defenses and ensure resilience against real-world threats.
05
Monitoring & Ongoing Support
Continuous monitoring, updates, and expert support help maintain security, adapt to new risks, and ensure long-term protection.
06
Continuous Improvement
Ongoing monitoring, optimization, and advisory support keep your security posture strong and up to date.
Build a Safer Digital Environment
Implement proven cybersecurity frameworks that protect people, systems, and sensitive information.
Frequently Asked Questions
What can I expect during the initial cybersecurity consultation with MMC Global?
+
During the initial consultation, our cybersecurity experts will conduct a thorough assessment of your current security posture. This includes identifying vulnerabilities, evaluating your existing security measures, and understanding your business objectives. We will then provide you with a detailed report outlining our findings and recommendations for enhancing your cybersecurity defenses. The goal is to create a tailored strategy that aligns with your specific needs and regulatory requirements.
How often should penetration testing be conducted?
+
Penetration testing should be conducted at least annually or whenever significant changes are made to your network or systems, such as after a major update or the implementation of new infrastructure. Regular testing helps ensure that new vulnerabilities are promptly identified and addressed, maintaining the integrity and security of your systems. Additionally, more frequent testing may be required for organizations in highly regulated industries or those handling sensitive data.
Why do we need to implement cybersecurity?
+
With the implementation of cybersecurity, businesses can reduce the risk of unauthorized access, data breaches, and insider threats. By implementing robust practices, your organization can enhance compliance with regulatory standards and improve overall security posture, making it harder for attackers to exploit weaknesses in your access controls.
Got Something on Your Mind? Let’s Make It Happen!
Fill out this quick form, and let’s make something amazing together! Whether it’s a question, an idea, or just a hello—we’re here to listen and respond. Start your digital transformation journey with us today!
Get A Free Consultation
